The Point-Solution Trap
The Derating of Cybersecurity’s Middle Class
Affiliation Disclosure & Disclaimer:
The managing principal of Ridire Research is affiliated with a private investment fund that holds short positions in the securities discussed herein (RPD, TENB, QLYS, FROG), which could influence the views expressed. This publication is for educational and informational purposes only. Any performance referenced is illustrative and tracked on a per-article basis, not as part of a model portfolio or investment program. Nothing herein constitutes investment advice, a recommendation, or a solicitation. → Ridire Research Substack Disclaimer
Table of Contents
Executive Summary
Company Overviews
Casual Mechanism
Key Risks
Conclusion
Executive Summary
The market is likely getting the direction of cybersecurity spending right, but the distribution wrong. AI should increase security budgets. Agents, non-human identities, AI-generated code, data leakage, prompt injection, runtime model abuse, and automated workflows all expand the enterprise attack surface.
But the more important question is not whether cybersecurity spending grows. It is who captures the incremental dollar.
Our view is that the next leg of security spending increasingly accrues to broad platforms that can unify identity, data, cloud, code, AI runtime behavior, and policy enforcement into a single control plane. That structurally disadvantages narrower point-solution vendors whose products solve important, but increasingly subscale, pieces of the problem.
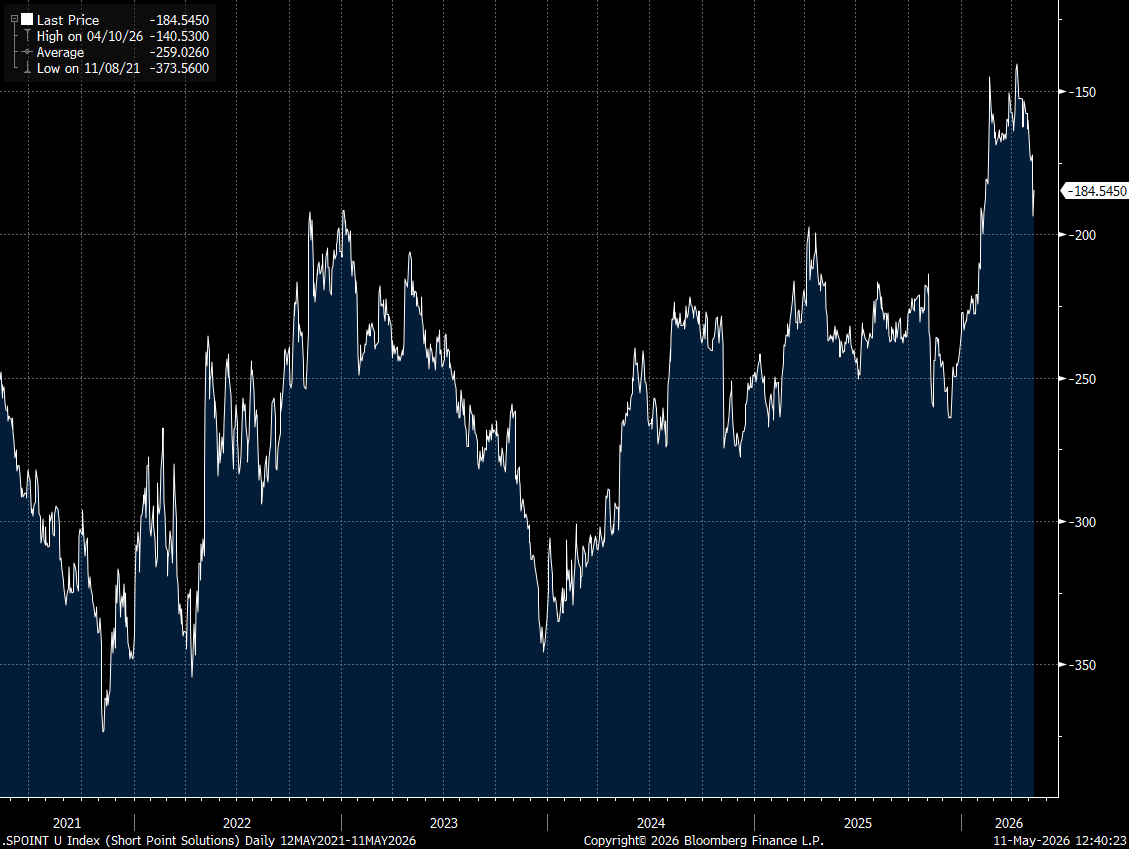
This creates a short opportunity in an equal-weight basket of:
TENB — Tenable
RPD — Rapid7
QLYS — Qualys
FROG — JFrog
These are not “zero” businesses. They have real products, real customers, and real recurring revenue. The short thesis is more subtle:
They can remain useful while becoming less strategic.
That is where software multiple compression happens. The product still matters, but the market stops valuing it as a control point. The AI security era does not reward another dashboard, another scanner, another compliance workflow, or another isolated DevSecOps tool. It rewards the platform that can answer a higher-order question:
What is the real business risk of this identity, workload, code change, data flow, or AI-agent action, and should it be allowed?
That answer requires integrated context. Integrated context favors platforms. Platforms compress point solutions.
Company Overview
TENB — Tenable
Tenable is primarily a vulnerability and exposure management company. Its core historical value proposition is visibility: helping enterprises understand where vulnerabilities, misconfigurations, and exposures exist across their environment.
That was a strong category in a world where visibility itself was scarce. (Worth noting here for any bulls reading that TENB is in our view the best company relatively speaking in this basket)
But the category is moving from vulnerability identification toward automated, contextual risk prioritization and enforcement. The buyer wants an integrated risk graph that understands cloud posture, identity privileges, runtime exposure, sensitive data, asset criticality, and remediation priority.
A scanner says:
“This asset has a vulnerability.”
A modern control plane says:
“This externally reachable workload contains sensitive data, has excessive permissions, is tied to a privileged identity, and should be remediated before lower-severity findings.”
Tenable’s 2025 filings already show the nuance: revenue still grew 11% to $999.4 million, but new enterprise platform customer additions were 1,667 in 2025, down from 1,689 in 2024 and 1,788 in 2023. Customers with $100K+ annual contract value did grow to 2,161, but the new-customer trend is not screaming greenfield acceleration. The business remains real, but the question becomes whether Tenable is the future control plane or simply one signal source feeding someone else’s platform.
RPD — Rapid7
Rapid7 sits in an increasingly uncomfortable middle ground. It has useful products across vulnerability management, detection and response, security analytics, and SecOps workflows. But in the current market, being “somewhat broad” is not the same as owning the platform.
The future security architecture is less about aggregating alerts and more about enforcing policy across live systems. That requires identity context, cloud context, endpoint telemetry, data sensitivity, AI runtime behavior, and automated remediation.
The company’s own numbers make this the cleanest expression of the basket. Rapid7 exited 2025 with $860 million of revenue, up only 2% year over year, and $840 million of ARR, flat year over year. Its initial 2026 guide called for full-year revenue of $835–843 million, implying a 2–3% decline.
Then in Q1 2026, ARR declined 0.6% year over year to $832 million, and full-year revenue guidance remained roughly $836–842 million, again implying a 2–3% decline.
That does not mean Rapid7 disappears. It means the company may already be showing what point-solution compression looks like when the market demands broader platform ownership: stable relevance, weaker growth, and a harder narrative.
QLYS — Qualys
Qualys is the classic durable-but-less-strategic risk. The company has a strong legacy franchise in vulnerability management, compliance, and cloud-based security assessment. Its installed base is real. Its renewal base is likely more durable than the most aggressive bears assume.
But durability is not the same as incremental relevance.
Qualys generated $669.1 million of 2025 revenue, up 10% year over year, with an extremely strong 47% adjusted EBITDA margin and operating cash flow equal to 46% of revenue.
That is not a broken business. It is almost the opposite.
The issue is that Qualys increasingly looks like a very profitable mature security utility at the exact moment the market is trying to identify the next strategic AI security control plane. The company has over 10,000 customers worldwide, including a majority of the Forbes Global 100, and no customer accounted for more than 10% of revenue in 2025.
That scale is a real asset. But it also frames the short case correctly: the debate is not survival. The debate is whether the market should pay a platform multiple for a company whose growth profile is increasingly mature.
The real risk is reclassification. Qualys may move from “strategic security platform” to “mature scanning and compliance utility.” In software, that distinction matters enormously for valuation.
FROG — JFrog
JFrog is different from the other three because it sits closer to the software supply chain and DevSecOps layer. That gives it a real bull case: AI-generated code increases code volume, dependency usage, package risk, and release velocity. In theory, that should increase demand for software supply chain security.
The numbers reflect that stronger fundamental setup. JFrog grew fiscal 2025 revenue 24% to $531.8 million. Cloud revenue grew 42% in Q4 2025 and represented 48% of total revenue. Net dollar retention was 119%, customers with more than $1 million of ARR rose to 74 from 52, and customers with more than $100K of ARR rose to 1,168 from 1,018.
So FROG is the least “obvious” short in the basket on near-term fundamentals.
But that is exactly why it belongs in the basket. The issue is not whether software supply chain security matters. It does. The issue is whether JFrog owns the control plane or becomes attached infrastructure inside someone else’s developer workflow.
If AI-assisted development becomes increasingly centered around GitHub, GitLab, hyperscaler CI/CD, cloud-native developer platforms, and AI coding environments, standalone DevSecOps vendors may lose platform independence.
JFrog may grow. The question is whether the market eventually decides the strategic control point migrated elsewhere.
Causal Mechanism
1. Best-of-breed becomes best-integrated
The prior cycle rewarded category depth. The next cycle rewards cross-domain context.
Agentic security requires a system that can understand:
who or what is acting,
what data is being touched,
what privileges are involved,
what code or workload is affected,
what the runtime behavior looks like,
and whether the action should be blocked, allowed, or remediated.
A narrow tool can provide signal. But the platform that correlates the signal and enforces the decision captures the economics. That is the core risk for this basket. TENB, RPD, QLYS, and FROG may provide useful inputs. But the market increasingly pays for the control plane, not the input.
2. “Good enough and already installed” becomes lethal
Enterprise buyers do not always choose the best product. They often choose the product that is already deployed, already approved, already integrated, already budgeted, and good enough. That favors companies like Microsoft, Palo Alto, CrowdStrike, Zscaler, Cloudflare, Google/Wiz, and other broad platforms.
A bundled product does not need to be perfect. It only needs to be good enough to make the standalone vendor justify:
another vendor review,
another contract,
another agent,
another dashboard,
another integration,
and another renewal.
That is a much harder sale than “we are the best product in the category.”
3. AI compresses the labor value of narrow workflows
A lot of legacy security software monetized analyst labor. It helped teams triage alerts, prioritize vulnerabilities, create tickets, document compliance, or manage workflows. AI can automate more of that labor layer.
As AI summarizes vulnerabilities, generates remediation steps, writes patches, classifies alerts, maps dependencies, and automates workflows, the value shifts away from tools that merely identify or organize problems.
The value shifts toward platforms that can close the loop:
detect → prioritize → decide → enforce → remediate.
Point tools that stop at detection or workflow management risk losing pricing power.
4. Incremental budget moves to newer control layers
The fastest-growing areas of security are likely to be:
AI runtime protection,
non-human identity security,
data security posture management,
cloud-native exposure management,
software supply chain enforcement,
and agent policy orchestration.
The issue is that these categories increasingly converge, for example:
AI runtime security needs data context.
Data security needs identity context.
Identity governance needs behavioral context.
Cloud posture needs runtime context.
DevSecOps needs production feedback.
The overlap becomes the product. That overlap is difficult for narrow vendors to own without broad telemetry, distribution, and enforcement rights.
5. Multiple compression can happen before fundamentals break
This is the most important point. The basket does not require immediate revenue collapse. These companies can still grow. They can still renew customers. They can still print respectable margins. But if investors decide the terminal value of the category is lower, the multiple can compress first.
That is classic software derating:
revenue remains real,
product remains useful,
customers remain sticky,
but strategic scarcity declines.
Key Risks
1. The basket companies successfully broaden
TENB, RPD, QLYS, or FROG could expand into broader platforms themselves. They have customers, brands, data, and engineering talent. If they credibly move from narrow workflows into integrated control planes, the short case weakens.
2. Best-of-breed remains resilient
Security buyers often distrust bundles. In high-stakes environments, “good enough” may not be acceptable. If specialist depth continues to matter more than integration, point solutions can persist longer than expected.
3. M&A risk
Any of these names could become acquisition targets for larger platforms seeking customers, telemetry, developer workflows, or category credibility. That creates obvious short-squeeze risk.
4. AI creates more fragmentation, not less
Cybersecurity history often favors more tools, not fewer. If AI creates many new subcategories rather than consolidated architectures, point vendors may find new growth vectors.
5. Timing risk
Enterprise security displacement is slow. Installed bases are sticky. Compliance workflows do not disappear overnight. The thesis may be right directionally but take years to express.
Conclusion
This is an equal-weight short basket of TENB, RPD, QLYS, and FROG. The thesis is not that these are bad companies. It is not that their products stop working. It is not that cybersecurity spending declines. Rather that AI changes the architecture of security. The market is moving from fragmented point tools toward integrated control planes that combine identity, data, cloud, code, runtime behavior, and automated enforcement.
That shift favors broad platforms and compresses standalone vendors.
The most dangerous version of software disruption is not when a product becomes less scarce. That is the risk here. TENB, RPD, QLYS, and FROG may remain useful. But in the AI security era, usefulness is not enough. The premium accrues to whoever owns the control plane.